Microsoft’s Push to Upgrade to Windows 11
Beginning in late 2021, Microsoft began to send out a program with their monthly Windows 10 Updates called Microsoft Update Health Tools.
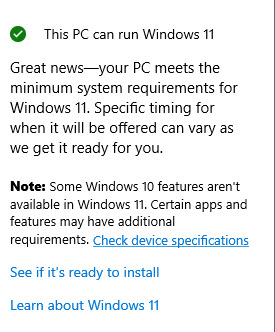
One of the functions of this program is to examine the hardware and software environment of the computer and determined whether or not it was ready for Windows 11. It would then show a message in the Updates and Security section of Settings advising if the PC was “Windows 11 ready”.
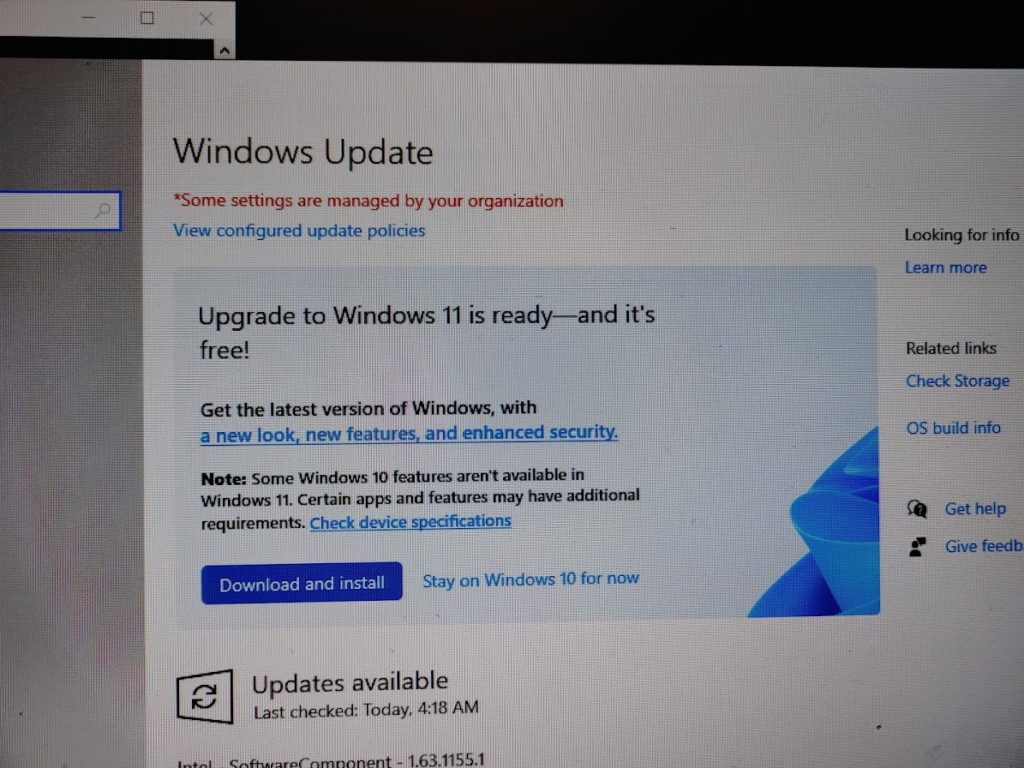
The user could choose between “Download and Install” or “Stay on Windows 10 for now”. If the latter was chosen, this would come up:
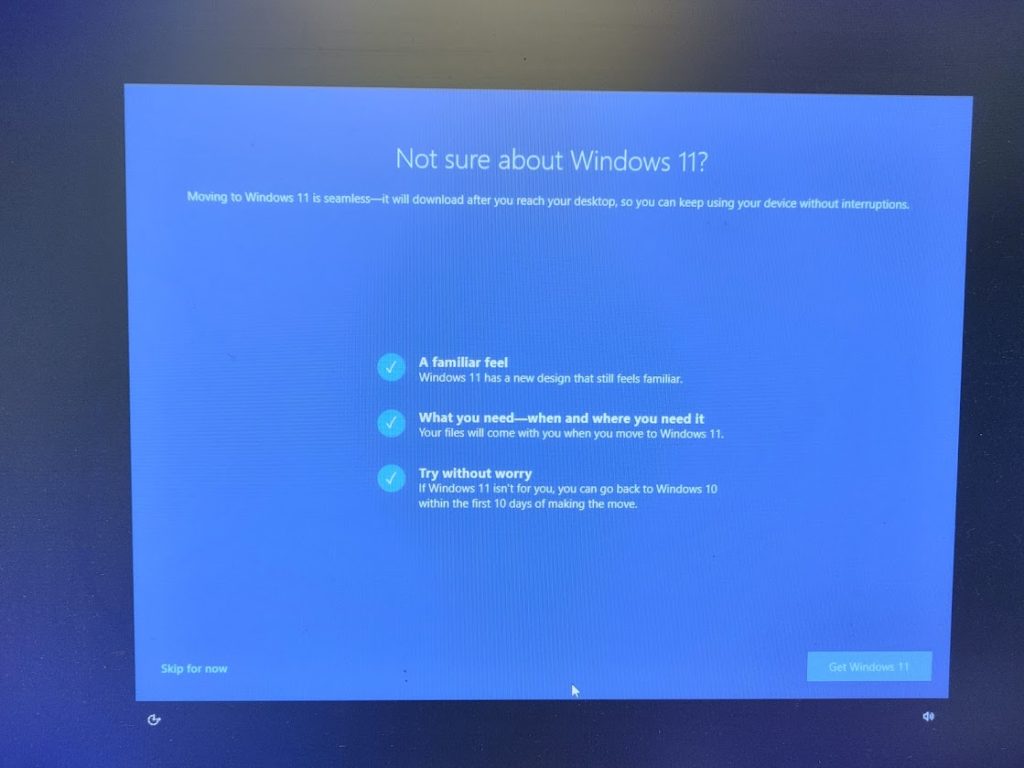
The user could choose between “Skip for now” or “Get Windows 11”. If “Skip for now” was chosen, then this would come up:

Microsoft is giving the user one more chance to upgrade, saying that they “recommend it for your device”. Once again, the user can “Decline upgrade” or “Get it”.
If “Decline upgrade” is chosen, the next time the user opened up “Updates and Security”, this would show, giving the user the ability to install Windows 11.
Why Not Upgrade?
OK, so, if your PC meets the requirements for Windows 11, and it doesn’t cost anything more, why not upgrade? Especially if you can revert to Windows 10 within 10 days (after 10 days you can no longer revert to Windows 10 unless you do a clean install of the OS, which means that all data will need to be backed up and all programs will need to be reinstalled, then data will have to be restored from the backup).
Here is a good article outlining the pros and cons of Windows 11. Probably one of the biggest cons is that not all apps/programs that are Windows 10 compatible are Windows 11 compatible. This was an issue when Windows 10 replaced Windows 7. This means that you’ll need to purchase new programs/apps to replace those that aren’t compatible, unless the software manufacturer offers a free upgrade.
Another con is going to be the interface. We’ve noticed some things that were in Windows 10 are not available in Windows 11. That’s OK if you didn’t use them, but not good if you did.
One item that we didn’t like when it came to a new PC with Windows 11 Home is that you could not create a local account initially when setting the PC up. You are forced to use a Microsoft account, unless you use Method 2 in this article, which can be complex.
Summary
PC Medics of Alabama/PCMDX believes in security most of all. We want to make sure that your environment, whether you’re a business or residential user, is safe from outside threats. This is why we won’t work on a Windows 7 (or older) PC. Windows 7 is no longer supported by Microsoft, thus is open to vulnerabilities. Ease of use, although important, is secondary to security.
Once Windows 10 is no longer supported by Microsoft, we will shift our focus to Windows 11. For now that’s years away. So, the choice to upgrade is yours. Sometimes the “if it ain’t broke, why fix it?” mindset is not so bad. Do you need the “latest and greatest” (which is subjective) or are things good for now?
Microsoft would have you believe that Windows 11 is awesome. Maybe it is. But, like all new operating systems, there are flaws that are not discovered until the OS is in the mainstream. Beta testing does not always reveal everything, especially since there are so many hardware platforms out there. Unlike Apple OS X (and now OS XI), where there’s only one hardware manufacturer, Apple, with Windows there’s thousands of hardware possibilities when you include motherboards, CPUs, GPUs, RAM, hard drives, etc., which means there could be thousands of compatibility issues.
So the choice is yours. Our PCs are staying on Windows 10 for now.