This post is a very long one, but it’s important you read every word if your data is important.
If you follow us on Facebook.com/pcmdx you know we’ve posted twice over the past month about ransomware attacks that we’ve been called to.
The attacks usually use the same method. The user will receive an e-mail from an unknown sender and it will have the subject line of “Invoice Attached” or something similar. The word invoice is the common denominator.
The user will look at the e-mail and see that it asks them to open the attached Word document, which is the “invoice”. When they open the document, the ransomware attack begins, however, it is not noticeable to the user.
These particular attacks encrypted all of the users Office files (Excel, Word, Powerpoint, Access, Outlook PST) files. It did not encrypt any PDF files or any image files, which usually would have been encrypted as well.
The user will notice that the attack has taken place when they attempt to open one of the files and the Windows program selector launches. This is the Windows feature that comes up when you attempt to open a file and no program is associated with it, meaning it doesn’t know what program to use to open the file and it asks you to choose one. In this case, there’s no program to launch an encrypted file.
We were called to attempt to recover the files and to remove the malware that encrypted the files.
The ransomware senders (we’ll call them the “bad guys”), usually have the ransomware program generate a text file that it leaves in each directory that has files that were encrypted. We found this text file in all of the directories with Office files, as well as the Desktop.
The text file is the “ransom note”. It explains what happened to the user’s files, and details how the files can be decrypted back to a usable state.
In a nutshell, the bad guys want a payment made via Bitcoin, usually ranging from a few hundred dollars to several thousand.
Although not always the case, once the ransom is paid, the decryption code is sent via e-mail. Once the code is entered, the files are decrypted and are usable again. It should be noted that this is some of the time, not all of the time.
In two of the cases, the ransom was not paid and the users accepted the fact that the files were gone.
In one of the cases the user felt that they needed the files, there was no backup, so they agreed to pay the ransom, although we recommended against doing so. The payment process took about three hours to complete.
It included opening a Bitcoin wallet, which is a software based wallet. Once the wallet was created, Bitcoin needed to be purchased. We found a seller in Tennessee who would sell the amount of Bitcoin needed (B 0.74, which was about $350, the amount of the ransom). Since there’s a trust issue between seller and buyer, the only way to pay the seller was to go to a Western Union type facility and wire the money. In this particular case, the Walmart 2 Walmart method was chosen. For those of you who don’t know what that is (and we didn’t know until this episode), you go to Walmart, fill out a form with the recipient’s name, address and phone number, give Walmart the cash amount, they then wire it to the Walmart closest to the recipient, who then picks it up.
Once the seller has been paid, he places the Bitcoin in an electronic escrow account, which the Bitcoin buyer then accesses and sends to his electronic wallet. Once this has been completed, he sends the ransom Bitcoin amount to the wallet of the bad guys, which is given to him in the ransom note. Once the bad guys confirm receipt, they provide a program to decrypt the files. If this sounds complicated, it is. Very complicated.
With this client, we received the decrypt program, ran it and it responded that the ransom had not been paid, therefore it shut down, without decrypting any files.
As odd as this may sound, the bad guys did have a “support” form on their web site where one could ask for help if the files didn’t decrypt. We used this form and they responded by asking that we submit five of the encrypted files to them and they would send a new decrypt program. Based on the timestamp of the response, we determined that they were in western Europe.
They provided a web site address to send the files to, but it required their e-mail address in order to send, which they refused to give, so we were unable to send the files. After a back and forth requesting their e-mail address, they blocked any further conversation, so the episode was closed.
The client lost his files. The client lost his ransom money. The moral of the story is DON’T PAY THE RANSOM AND MAKE SURE YOUR FILES ARE BACKED UP! (PCMDX had recommended that they do not pay the ransom, however the client insisted).
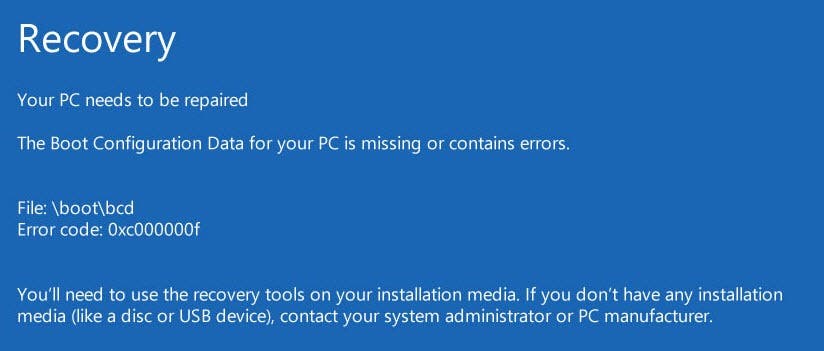
The latest type of ransomware goes a step further. It doesn’t encrypt the files. It encrypts the entire hard drive, so nothing is usable. Unless you have an backup image of your hard drive, you won’t even be able to log into Windows.
So what can you do to prevent ransomware from ruining your day, or your year?
First, ask yourself one simple question: “Is there anything on my computer that I cannot absolutely, positively live without?” If the answer is “Yes”, then you need to take steps to protect yourself against malware (including viruses, ransomware, Trojans, worms, rootkits, etc), hardware failures, data theft, and other data losing issues.
The very first thing you need to do is to make sure you have a backup of your system. PCMDX uses and installs two backup strategies, an image based backup and a file based backup.
An image based backup consists of an image, or “picture”, of you hard drive. The backup software makes an exact replica of your hard drive. In the event of failure or loss, the backup software recreates the hard drive onto another hard drive. Think of it like cloning your hard drive.
PCMDX believes this to be a better system for one main reason: time savings.
A conventional backup copies only the data from a hard drive. Let’s say there’s a failure of the hard drive. Here’s the recovery steps: reinstall the hard drive, reinstall the operating system, reinstall the updates and patches, reinstall the programs, copy the data from the backup. This could take hours, perhaps days until completed.
If there’s a hardware failure on a computer with an imaged backup, here’s the recovery steps: reinstall the hard drive, insert rescue disk, point to image location, begin restoration. 45-60 minutes later it’s like nothing happened to the computer in the first place. Everything is as it was when the image was created.
Depending on the software used, individual files can also be recovered from an image. This is great if a user accidentally deletes a file.
The cost of setting up a backup system is less than what would be paid if there’s a ransomware attack.
We cannot emphasize the two following points enough:
- Have a backup plan in place. If you don’t know how to implement one, call PCMDX today. We’re not talking about backing up one or two files on a thumbdrive (although that’s better than nothing). We’re talking about backing up your system, and other systems in your network in case of disaster. Again, if you answer the question “Is there anything on this computer that I cannot live without” with a “yes” answer, and you don’t have a backup plan in place, you need to create one today.
- NEVER open any attachments from senders you don’t know, from senders you’re not expecting anything from, from e-mails that are vague in nature or have spelling and/or grammar errors in the body of the e-mail. If in doubt, call the sender and ask them if they sent you an attachment.
- If you’re hit, DON’T PAY THE RANSOM. Our latest experience proves that even after you pay it, you’re dealing with people who have no ethics, no morals, no sense of right and wrong, and very poor command of the English language. Your files are lost and paying the ransom simply adds to the cost of fixing the problem without recovering your data.
One other bit of information: If your PC is on a business network, and you have networked drives (places on a server where you can access your files), including Dropbox, OneDrive, and Google Drive, those files can be encrypted as well. Make sure they are also part of the backup plan.
Feel free to share this with your friends.