It has been several months now that Windows 10 has been on the market. Most PCs that you buy today in stores are going to no longer come with Windows 8.1 with the free upgrade, but with Windows 10 pre-installed.
PCMDX has been working with several Windows 10 computers, including laptops, tablets, and workstations.
Based on what we’ve learned, our recommendation at this time is as follows:
If you have Windows 7, stay there. You don’t need to upgrade just yet, and some programs (now also known as “Apps” or “Applications”) may not work in Windows 10, even though they do work in Windows 7 or 8. Many vendors who’s programs don’t work on Windows 10 simply state that they don’t support it, therefore if it doesn’t work, they can’t help you.
Windows 10 has a “revert back to previous OS” feature. You only have 30 days from the upgrade to rollback, and many users claim that this feature does not work when they try it. We’ve also found it not to work on PCs that we’ve attempted a rollback on.
If you have Windows 8, read on. In our opinion, Windows 10 is a clear upgrade to Windows 8. It’s really a cross between all that’s good about Windows 7 and Windows 8. The most asked for feature is back, the Start menu, but it will take some time to get used to, with some of the changes. If you’re running programs on Windows 8, you may have a problem running them on Windows 10 if the program vendor has not released an update.
Our biggest issue with Windows 10 is the lack of controlling Windows Updates (WU) without going into some complex settings. With previous versions of Windows, you were given several options when it came to WU. You could turn WU off altogether (not recommended). You could be notified of WU being available, but not download and install them until you’re ready. You could download them and be notified when they are ready to be installed. Or you could simply let Windows download and install WU.
Windows 10 doesn’t give you these options. It simply updates on its own. Because it may require a reboot, it might give you an option to delay the reboot process if you’re currently working on something. But it will eventually reboot on its own.
We have a problem with this, and hopefully Microsoft will address it by going back to giving the user options. The reason we have a problem with this is because every once in a while, Microsoft will release an update that will negatively affect a PC. This has happened numerous times in the past two years. When updates are set to Automatically Download and Install Windows Updates, if the update is bad, the user will find that their PC might not function properly. The user then has to find a way to correct the issue. Usually Microsoft will withdraw the update within a few hours of it’s release.
Windows Updates are release on the second Tuesday of the month (which is referred to as “Patch Tuesday”). If there’s a critical update that needs to be installed, Microsoft will release it as needed, but that’s rare. On Patch Tuesday, all computers set to Automatically Update, will do so, usually around 3am. By 9am, if there’s a bad update, Microsoft will pull it, but it can take as long as the rest of the day.
We recommend setting your Windows Update settings to Notify but Don’t Download Updates. picking a day AFTER Patch Tuesday to do your updates, like the second Saturday. Then download and install the WU. This will give Microsoft time to remove the bad updates.
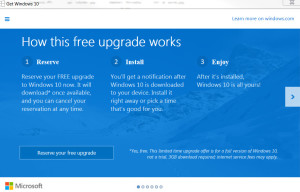
So, to summarize, we suggest waiting on Windows 10. If you do decide to do the upgrade, do so knowing that you may not be able to go back unless you do a fresh install of the previous operating system, which wipes out all of your settings, programs and data. Also, you may want to follow the instructions on doing a custom setup of Windows 10.
We’re still in the first year of Windows 10, so many features of the OS have still to be discovered. Check back often for Update 3.